Hunting the hunters: how to find airdrop hunters
Author: Isaac Lau
Historically, protocols and blockchain networks alike attract users and liquidity with the promise of tokens after product-market fit. These tokens represent two primary incentives:
- The ability to govern the direction of the product
- Monetary allocation
One of the most common criticisms of web2 is that its users have no ownership over the networks and applications that they contribute to and are a part of.
Web3 offers an alternative, community-based ownership model with tokens serving as a key part of this new paradigm.
Given the importance of a community-oriented mindset when thinking about token distribution, web3 projects seek to ensure they airdrop (i.e. distribute) tokens to active community participants who have a vested stake in the product’s success.
While there is an active and valid debate about who constitutes as an "active community member," there is one party that is objectively a bad actor—users and bots engaging in sybil attacks.
What is a sybil attack?
Sybil attacks use a single network node to operate many fake identities, often simultaneously, within a Peer-to-Peer (P2P) network.
A sybil attack leads to a small number of network actors gaining an undue share of influence, which in the context of an airdrop, means a larger share of governance tokens.
In terms of airdrop hunting, this means inauthentically interacting with protocols and contracts.
Hop exchange’s airdrop hunter strategy
While many past airdrops have yet to truly crack down on bad actors, Hop Exchange introduced a new mechanic that leverages its community members to reduce the impact of sybil attacks:
"We are accepting reports of Sybil addresses that have not yet been uncovered. When Hop DAO is live, we will make a proposal to reward those who reported Sybil addresses with 25% of the tokens saved — subject to a 1-year lockup. Reports will be reviewed, and rewards will be tallied on a first-come, first-serve basis."
As one of the first community-based initiatives that rewards hunters of airdrop hunters, Hop unleashed the full power of the web3 developer community, including myself.
Let’s dive into my contribution to the Hop DAO decentralization efforts.
Discovering airdrop hunters
This is graphical representation of the addresses I identified as part of a Sybil attack.
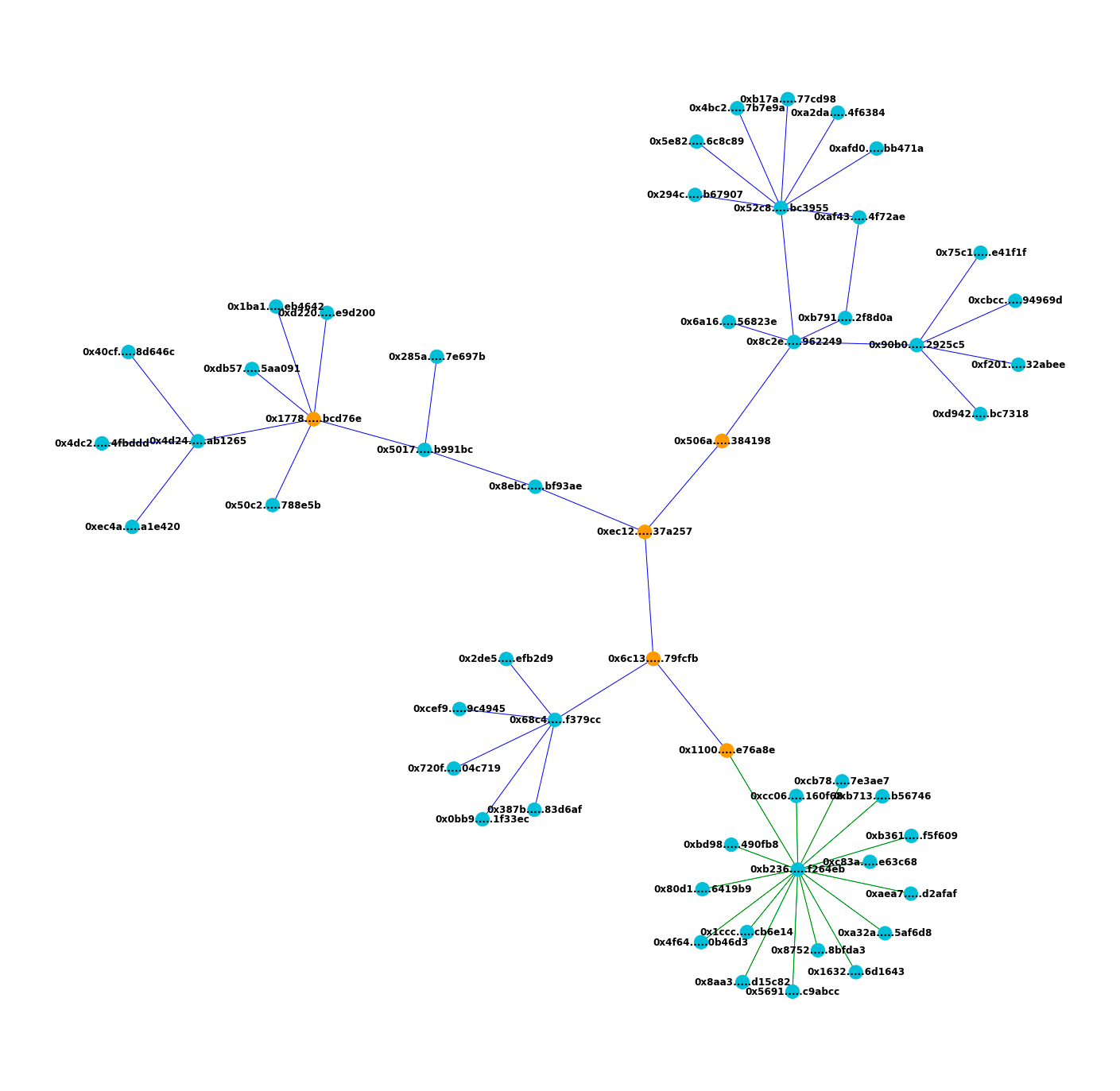
Here’s how to read the sybil attack visualization:
Each address is a node in the graph, and all shown addresses are connected by on-chain transfers between each address denoted by each edge.
The sybil attacker exhibits two distinct patterns with the blue-colored edges denoting pattern one and the green-colored edges denoting pattern two.
Orange-colored nodes denote addresses that serve as on-chain connections between all sybil accounts where transfers occurred, and are included in the submission set due to deviations from the two main patterns outlined in this report.
Pattern #1
All addresses connected by blue edges used Hop Exchange to ping-pong back-and-forth between Gnosis Chain (formerly xDai) and Polygon.
Each address prominently featured Hop transactions denominated in ~1000 $USDC (1 transaction in USDT) with a variable range of ± 250 dollars across the transactions, criss-crossing from one chain to another and back sequentially.
Furthermore, each batch of transactions within each address took place over a very small timespan (on the order 1-3 hrs).
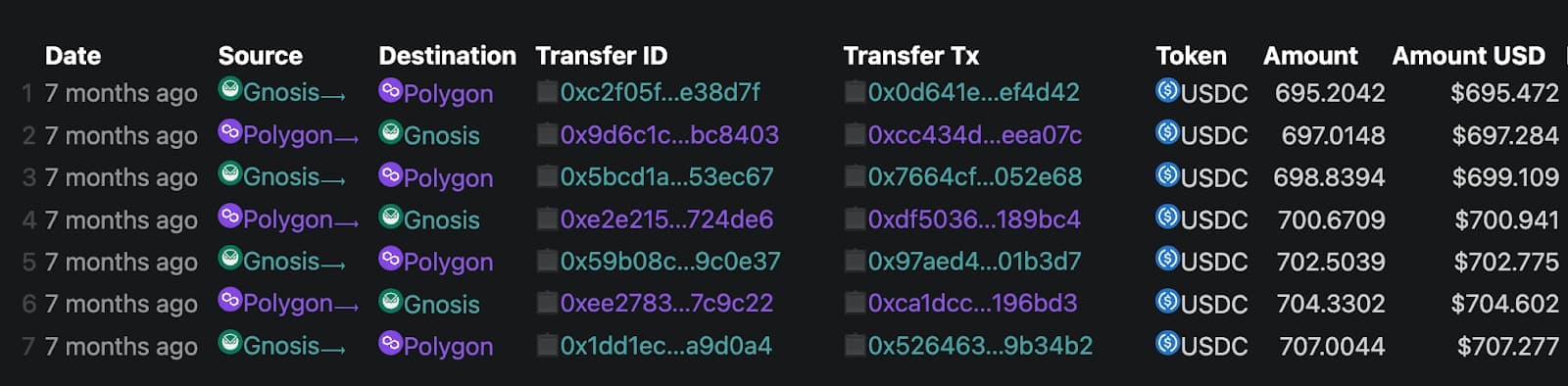
Here is an example of this behavior:
https://explorer.hop.exchange/?account=0x4bc25a712b87c1e4a42df9ffac3662fe467b7e9a
How was pattern #1 discovered?
Pattern #1 was found by tracing on-chain Ethereum transfers using the Alchemy Transfers API. Upon investigation, a connected set of addresses, namely Pattern #2, was connected to Pattern #1 by tracing transfers between the hub address (0xb23691043293de4deeae3b565bd33bc059f264eb) and its associated spokes on the Avalanche mainnet.
Pattern #2
For addresses connected by green edges, the attacking addresses used Hop Exchange multiple times over a period of several hours, conducting repeated exchanges primarily from Gnosis Chain (formerly xDai) to Polygon.
All transactions typically utilized $200-$300 dollars in $DAI, $USDC, or $USDT.
In aggregate, Pattern 2 occurred over the span of a week from Jan 15th, 2022 - Jan, 24th 2022.
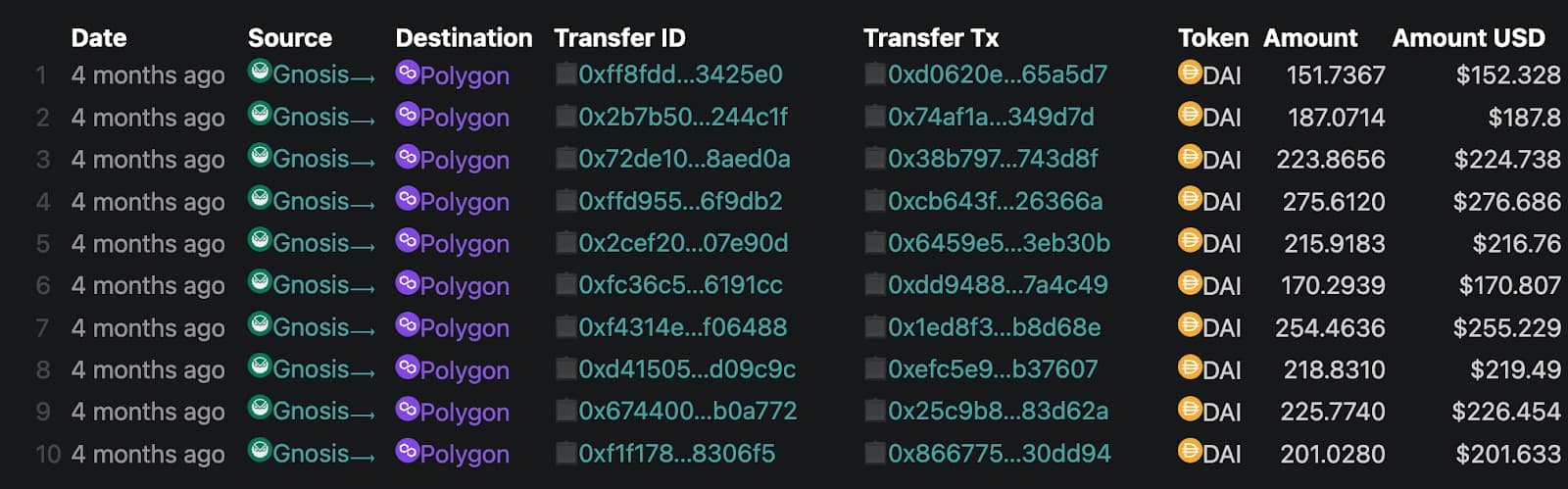
Here is an example of this behavior:
https://explorer.hop.exchange/?account=0x1cccff3de9b0a7c466acb31f33910691f1cb6e14
Connecting pattern #1 and pattern #2
Pattern #1 and #2 were found to be connected because the sybil attacker overlapped transactions on the Ethereum mainnet and the Avalanche mainnet.
Specifically, transfers between these addresses occurred on both networks denoting the connection in the two patterns.
- 0x1100cc….d34e76a8e ←→ 0xb2369….59f264eb
- 0xb23691….f264eb ←→ 0x80d….19b9
With over 30,000 addresses to comb through, it was challenging to find a connected subset, but the Transfers API was able to effectively trace transactions on Ethereum.
How to find airdrop hunters
By searching the transfer history of all eligible addresses on Ethereum and Avalanche mainnet, we are able to trace shared on-chain activity to discover connected addresses.
To reduce the amount of brute-force computation required to find eligible addresses, we reduced the cluster search size by rejecting clusters with a low number of shared addresses.
After filtering out unlikely addresses, we queried Hop Exchange subgraphs across each of Hop’s different supported blockchains to generate a basic profile of each address cluster.
If a cluster profile had repeated address behavior, it was earmarked for manual verification.
How can I hunt airdrop hunters?
With a free Alchemy account, Etherscan API keys, access to subgraphs, and some basic Python scripting, you can become a hunter of airdrop hunters.
Feel free to reach out to me on Twitter (@crypt0zeke) if you have good strategies for finding airdrop hunters, are interested in crypto research, or want to chat about web3 projects.
Until then, keep an eye out for new community initiatives and I'll catch all of you on the next hunt!
Alchemy Newsletter
Be the first to know about releases
Sign up for our newsletter
Get the latest product updates and resources from Alchemy
By entering your email address, you agree to receive our marketing communications and product updates. You acknowledge that Alchemy processes the information we receive in accordance with our Privacy Notice. You can unsubscribe anytime.
Related articles

The complete guide to Solana for financial institutions
BlackRock, Franklin Templeton, and major banks are deploying on Solana. Here’s why institutions are choosing the network, how multi-chain operations change the calculus, and what to demand from infrastructure providers.
x402 vs MPP: comparing agent payment protocols
x402 and MPP both let AI agents pay for API calls over HTTP, but they differ in payment rails, session support, and protocol-level primitives. Here's how they compare.
The infrastructure behind the world's leading blockchain applications
Alchemy processes billions of blockchain requests daily for companies like Visa, Stripe, and Coinbase. Here's how eight years of engineering built the infrastructure behind $150B+ in annual onchain transactions across 100+ chains.